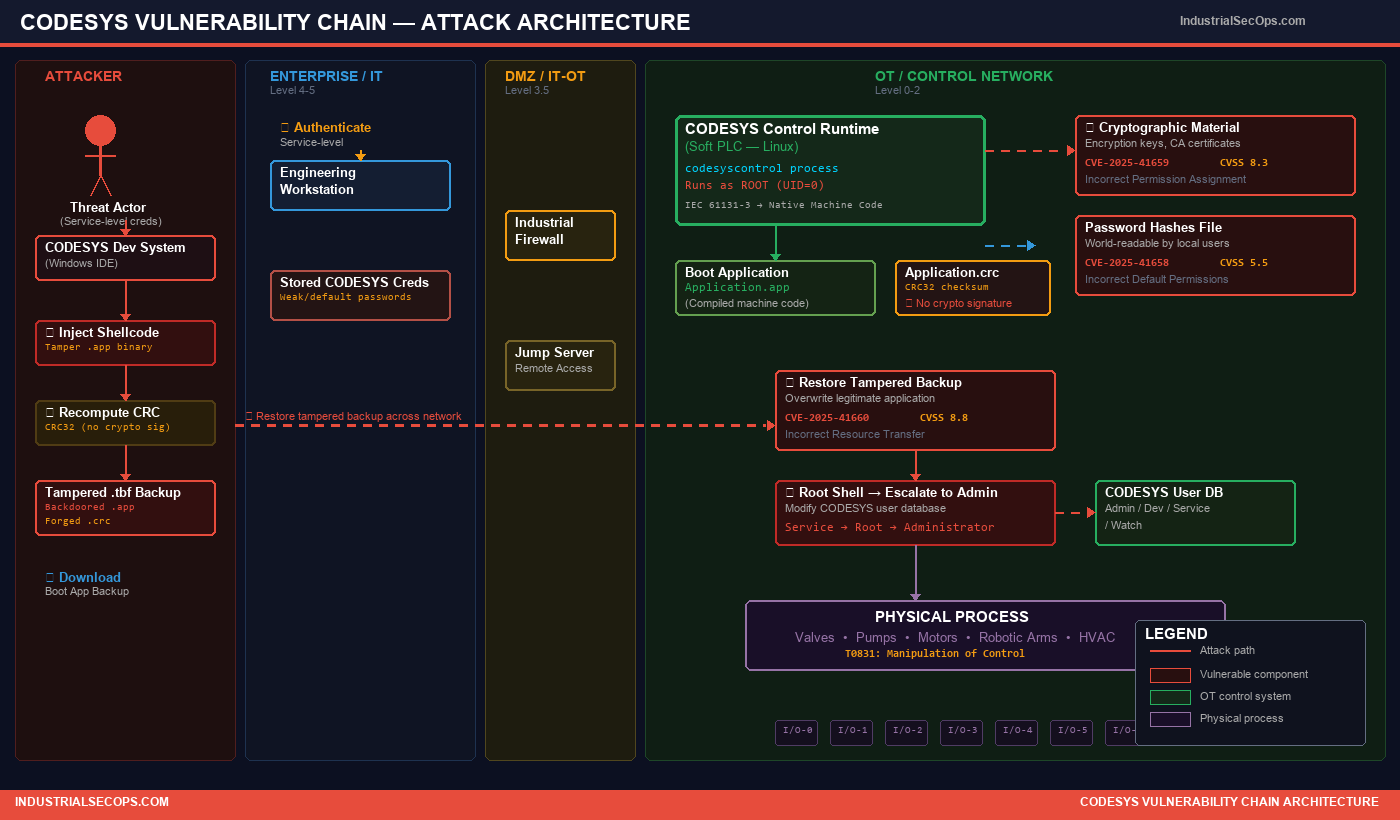
Backdooring PLCs at Scale: How Three CODESYS Vulnerabilities Let Attackers Own Industrial Control
IndustrialSecOps Research · May 2026 · 8 min read
Tags: ICS Security, PLC, CODESYS, Vulnerability Research, Soft PLC, Supply Chain, OT Security
⚡ TL;DR for Defenders
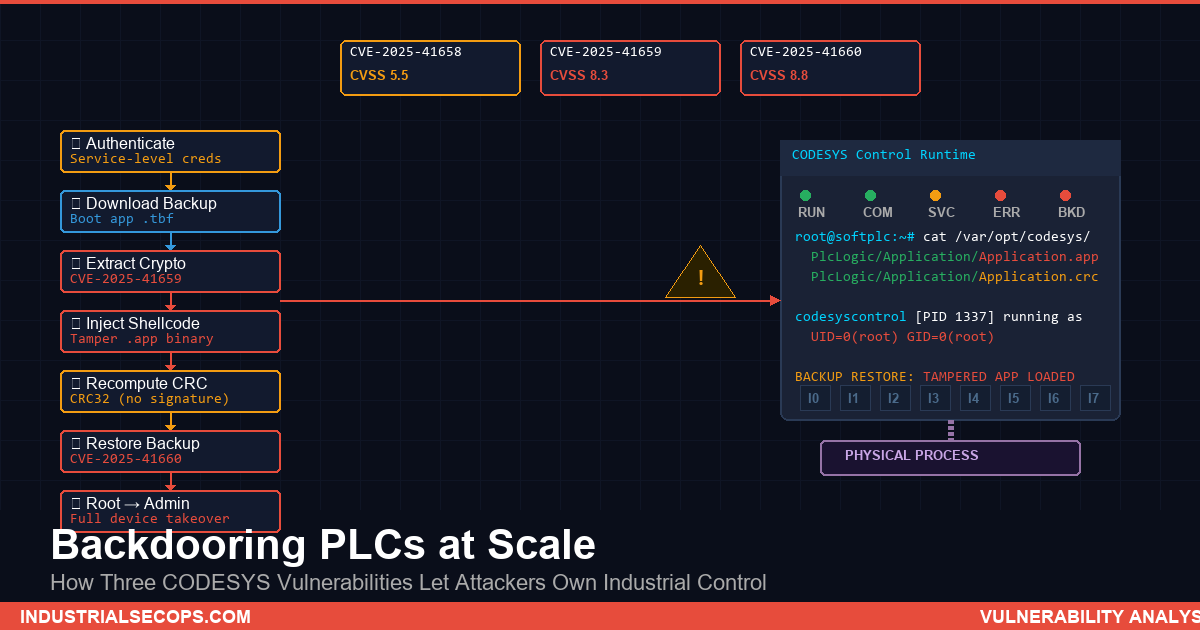
Three newly disclosed vulnerabilities in the CODESYS Control runtime (CVE-2025-41658, CVE-2025-41659, CVE-2025-41660) allow an authenticated attacker with low-privilege Service-level credentials to backdoor PLC applications, escalate to root, and seize full administrative control of the device. CODESYS powers Soft PLCs from hundreds of manufacturers — Beckhoff, WAGO, Schneider, ABB, and many others — making this one of the widest-impact ICS vulnerability chains disclosed in 2026. Patches are available. Apply them now.
1. What Happened
On April 23, 2026, Nozomi Networks Labs published detailed research into three chained vulnerabilities affecting the CODESYS Control runtime, the software engine at the heart of Soft PLCs used across manufacturing, energy, water treatment, and building automation worldwide.
CODESYS is not a single vendor’s product. It is a manufacturer-independent IEC 61131-3 development and runtime platform integrated by hundreds of device makers into their hardware. When security researchers find flaws in CODESYS, the blast radius spans an enormous cross-vendor footprint — from a single Raspberry Pi test bench to production-floor PLCs governing safety-critical processes.
The three CVEs discovered by Nozomi Labs are:
| CVE | Weakness | CVSS v3 |
|---|---|---|
| CVE-2025-41658 | Incorrect Default Permissions | 5.5 |
| CVE-2025-41659 | Incorrect Permission Assignment for Critical Resource | 8.3 |
| CVE-2025-41660 | Incorrect Resource Transfer Between Spheres | 8.8 |
Individually, each vulnerability represents a design weakness. Chained together, they form a complete privilege escalation pathway from a low-privilege Service user to root-level code execution and full device takeover.
2. Technical Breakdown — The Attack Chain
How CODESYS Works
The CODESYS ecosystem has two components: a Windows-based IDE (the Development System) where engineers write and compile IEC 61131-3 programs, and the Control runtime that executes those compiled applications on target hardware. The runtime compiles ladder logic, structured text, and other IEC languages directly into native machine code, then loads and runs that code in its own process — as root.
This is by design for administrators. The security question is what happens when a non-administrative user can abuse the same execution model.
The Privilege Model
CODESYS defines four default privilege levels: Administrator, Developer, Service, and Watch. Service users have intentionally broad access because they need to create and restore backups of deployed applications. That backup capability is the critical enabler for this attack.
The Seven-Step Chain
- Download the boot application. The attacker uses the Development System’s backup function to download the compiled
.appbinary and its CRC checksum file. - Access cryptographic material (CVE-2025-41659). Exploit incorrect permissions to retrieve encryption keys and certificate authority material from the device.
- Bypass cryptographic protections. Decrypt the application, modify it, re-encrypt it, and re-sign modified code using attacker-controlled trusted material.
- Tamper with the boot application. Inject shellcode into the compiled binary — a sophisticated attacker hooks a rarely executed branch to maintain stealth.
- Recompute the checksum. The
.crcfile uses simple CRC32 with no cryptographic signature — trivial to recalculate. - Restore the tampered backup (CVE-2025-41660). Upload the backdoored application to the device, overwriting the legitimate one.
- Wait for restart → root → Admin. On application restart, injected code executes as root. The attacker modifies the CODESYS user database to grant themselves Administrator privileges.
Local Access Bootstrapping (CVE-2025-41658)
If the attacker has local OS access but lacks CODESYS credentials, CVE-2025-41658 provides the entry point: incorrect default file permissions expose the file containing CODESYS password hashes to any local user, enabling offline credential extraction.
3. Who Is Affected
This is not a single-vendor problem. CODESYS Control runtimes are embedded in products from hundreds of manufacturers. Any device running an affected version is vulnerable, regardless of the hardware brand on the nameplate.
Robotic arms, conveyors, CNC machines
Generation, transmission, distribution controllers
Treatment automation, pump control
HVAC, elevator controls, fire suppression
All vulnerabilities are fixed in CODESYS Control Runtime v4.21.0.0 and Runtime Toolkit v3.5.22.0.
4. Why This Matters — The Supply Chain Amplifier
Most ICS vulnerability disclosures affect a single vendor’s product line. CODESYS is different. It functions as a shared software supply chain component — a runtime engine that device manufacturers license and integrate. A vulnerability in CODESYS is effectively a vulnerability in every product built on it.
This creates compounding challenges:
- Patch coordination complexity. CODESYS Group issues the fix, but each device manufacturer must validate, repackage, and distribute updates for their specific hardware. Some will be fast; others will take months.
- Asset visibility gaps. Many operators don’t know which devices run CODESYS under the hood. The brand on the HMI panel may say Beckhoff or WAGO — but the vulnerable runtime is the same.
- Long device lifecycles. Industrial controllers often run for 15–20 years. Devices deployed before these patches may never receive updates.
5. MITRE ATT&CK for ICS Mapping
| Technique | Relevance |
|---|---|
| T0839 — Module Firmware | Replacing the legitimate control application with a backdoored version |
| T0831 — Manipulation of Control | Changing setpoints, overriding safety interlocks, falsifying sensor readings |
| T0882 — Theft of Operational Information | Extracting compiled control logic, credentials, and cryptographic material |
| T0859 — Valid Accounts | Exploiting default or extracted credentials to authenticate as a Service user |
6. Defensive Recommendations
🔴 Immediate (This Week)
- Patch now. Update all CODESYS Control runtimes to v4.21.0.0 or later. Contact your device manufacturer for hardware-specific firmware updates.
- Inventory your CODESYS footprint. Many OEM products don’t advertise CODESYS branding — check firmware details and vendor documentation.
- Rotate Service-level credentials. Change any default or weak passwords immediately.
- Restrict network access. Limit connectivity to CODESYS management ports to designated engineering workstations on segmented networks.
🟡 Short-Term (30 Days)
- Enable code signing. Patched versions make it mandatory by default — verify enforcement in your deployment.
- Monitor backup/restore operations. Alert on unexpected backup downloads or restores outside maintenance windows.
- Audit privilege assignments. Review Service-level access justification across all accounts.
🟢 Long-Term (Ongoing)
- Deploy OT network monitoring. Detect CODESYS protocol activity, unauthorized connections, and anomalous behavior.
- Maintain an SBOM. Track shared runtime components across your device fleet for immediate impact assessment on future disclosures.
- Establish manufacturer patch SLAs. Set expectations with device vendors for turnaround time on embedded component security patches.
7. The Bigger Picture — Why Soft PLCs Change the Risk Equation
The shift from dedicated hardware PLCs to Soft PLCs delivers real operational benefits: lower costs, flexible deployment, easier updates. But it also changes the attack surface fundamentally.
A traditional hardware PLC runs proprietary firmware on a specialized processor. A Soft PLC runs compiled code on Linux — the same Linux attackers have spent decades learning to exploit. When that runtime process executes as root (as CODESYS does by design), every vulnerability in the runtime is a root-level vulnerability on the host OS.
This doesn’t mean Soft PLCs are inherently less secure. It means defenders must apply the same rigor to Soft PLC security that they would to any root-level service: least privilege, mandatory code signing, network segmentation, and continuous monitoring.
8. IndustrialSecOps Analyst Assessment
Severity: HIGH — Patch Immediately
This vulnerability chain represents one of the most impactful ICS disclosures of 2026 due to the cross-vendor footprint. The attack is not theoretical — Nozomi demonstrated a complete chain from Service-level access to root shell. The only limitation is that the attacker must wait for an application restart, a constraint that operational environments regularly satisfy through maintenance cycles, firmware updates, and routine reboots.
The remediation path (patching and enabling mandatory code signing) is clear, but the real challenge is the supply chain propagation delay. Organizations that rely solely on their device vendor’s patch cycle will remain exposed long after the CODESYS fix is available.
Bottom line: Know your CODESYS footprint. Patch what you can. Monitor what you cannot.
9. Sources and Further Reading
- Nozomi Networks Labs — Backdooring CODESYS Applications via Vulnerability Chaining (April 23, 2026)
- CVE-2025-41658 — CODESYS Advisory
- CVE-2025-41659 — CODESYS Advisory
- CVE-2025-41660 — CODESYS Advisory
- MITRE ATT&CK for ICS — T0839 Module Firmware
- MITRE ATT&CK for ICS — T0831 Manipulation of Control
- MITRE ATT&CK for ICS — T0882 Theft of Operational Information
IndustrialSecOps.com — Defending the systems that run the physical world.

Leave a Reply
You must be logged in to post a comment.