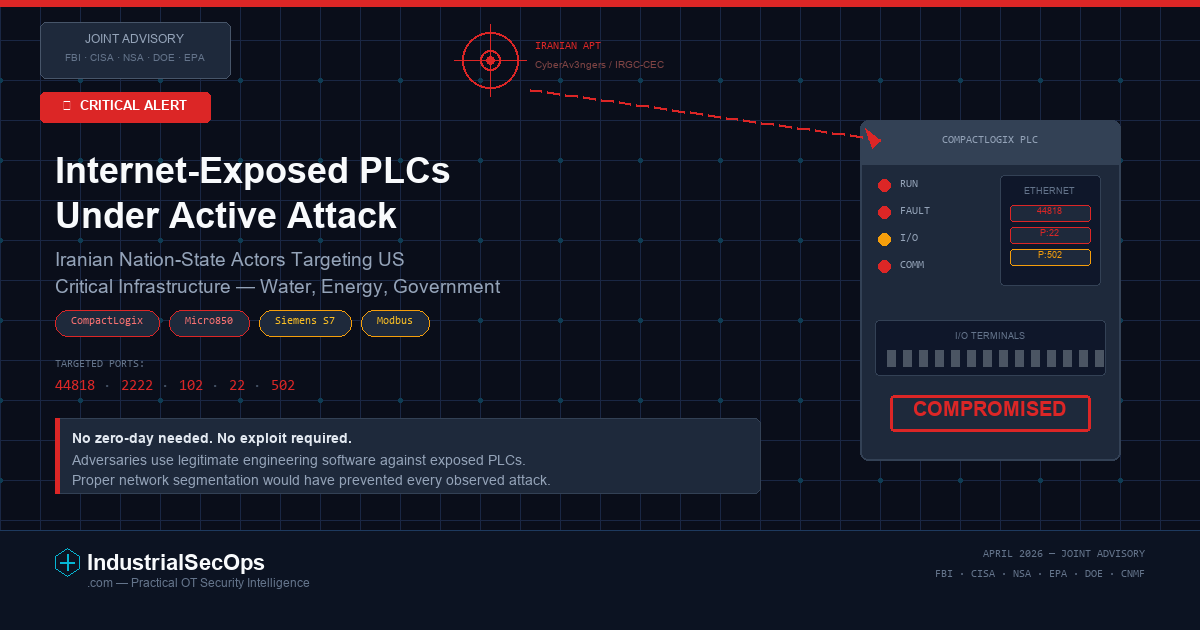
On April 8, 2026, a joint advisory from the FBI, CISA, NSA, EPA, DOE, and US Cyber Command confirmed that Iranian-affiliated advanced persistent threat (APT) actors are actively exploiting internet-connected programmable logic controllers (PLCs) across multiple US critical infrastructure sectors. The attacks — attributed to actors linked to the CyberAv3ngers group and Iran’s Islamic Revolutionary Guard Corps (IRGC) — have resulted in manipulation of HMI and SCADA displays, disruption of PLC operations, and confirmed cases of operational disruption and financial loss.
This is not a future threat scenario. It is happening now in production environments. OT defenders, plant managers, and security architects must treat this as an immediate action item.
What Happened
Since March 2026, US cybersecurity agencies have observed Iranian-affiliated APT actors using overseas-based IP addresses to access internet-facing Rockwell Automation/Allen-Bradley PLCs, specifically CompactLogix and Micro850 devices. The attackers leveraged leased, third-party hosted infrastructure along with legitimate configuration software, Rockwell Automation’s Studio 5000 Logix Designer, to establish accepted connections to victim PLCs.
Once connected, the adversaries:
- Maliciously interacted with PLC project files
- Manipulated data displayed on HMI and SCADA systems
- Disrupted PLC function in active operational environments
- Deployed Dropbear SSH software on victim endpoints for persistent remote access via port 22
Targeted communication ports include 44818 (EtherNet/IP), 2222, 102 (S7comm/Siemens), 22 (SSH), and 502 (Modbus). The targeting of ports associated with other vendors’ protocols, including Siemens S7 PLCs, indicates the campaign may extend beyond Rockwell Automation devices.
The affected sectors include water and wastewater systems (WWS), energy, and government services and facilities, including local municipalities. Some victims experienced confirmed operational disruption and financial losses.
Why This Matters for OT/ICS Environments
This advisory represents a significant escalation in nation-state targeting of operational technology. Several factors make this particularly concerning:
1. Direct PLC compromise, not just IT network intrusion
Unlike many OT-related incidents that stop at the enterprise or DMZ layer, this campaign involves direct manipulation of Level 1 control devices. The attacker is not simply stealing data — they are altering the physical process.
2. Legitimate tools used as attack vectors
The use of Studio 5000 Logix Designer — the same engineering software used by plant operators — makes detection significantly harder. The PLC sees a legitimate protocol handshake from legitimate software. Standard signature-based detection will miss this.
3. Internet exposure as the primary attack surface
Every compromised device was directly reachable from the internet. No zero-day exploit was needed. No sophisticated supply chain compromise. The adversaries simply connected to PLCs that should never have been exposed.
4. Geopolitical escalation driving operational risk
The advisory explicitly ties this activity to Iranian retaliation in response to US-Israeli hostilities. Critical infrastructure operators must assume elevated targeting during periods of geopolitical tension.
5. Cross-sector and cross-vendor implications
While the confirmed targets are Rockwell Automation devices, the port scanning activity against S7comm (Siemens), Modbus, and other protocols suggests the threat extends to any internet-exposed PLC or RTU, regardless of manufacturer.
High-Level Attacker Pathway Analysis
Note: This section provides a defensive, conceptual-level analysis of the attack path. No exploit code, payloads, commands, or weaponized procedures are included. The purpose is to help defenders understand where to validate controls.
The attack path observed in this campaign follows a disturbingly simple pattern:
Reconnaissance → Direct Access → Configuration Manipulation → Operational Impact
- Internet scanning and enumeration: Adversaries scan for internet-exposed devices on known ICS ports (44818, 502, 102, 2222). Publicly available search engines make this trivial.
- Trust boundary failure: PLCs exposed directly to the internet have no intermediary security control — no firewall, no jump host, no VPN, no authentication gateway. The attacker reaches the device as if they were on the local OT network.
- Legitimate protocol exploitation: Using commercially available engineering software (Studio 5000), the attacker establishes a connection that the PLC treats as a valid engineering session. There is no exploit — the PLC is functioning exactly as designed, accepting connections from any authorized client.
- Project file and logic manipulation: Once connected, the adversary can modify PLC project files. This allows changes to control logic, setpoints, alarm thresholds, or display values on connected HMIs.
- Persistent access via SSH: The deployment of Dropbear SSH on victim endpoints creates a backdoor for ongoing access, independent of the ICS protocols used for initial entry.
- Operational disruption: Altered logic or display values can cause incorrect operator actions, safety system failures, process disruptions, or equipment damage — without the operator being aware the system has been compromised.
What Defenders Should Validate Immediately
- Are any PLCs, RTUs, or ICS devices directly accessible from the internet? Scan your own external perimeter for ports 44818, 2222, 102, 22, and 502.
- Are engineering workstation connections to PLCs logged and monitored? Can you distinguish between a legitimate engineer and an unauthorized remote connection?
- Do PLCs require authentication before accepting configuration changes? Many legacy PLCs accept connections from any client running the correct software.
- Is remote access to OT environments routed through a hardened jump host with MFA? Or can someone with VPN credentials reach Level 1 devices directly?
- Are PLC project files baselined and monitored for unauthorized changes? Configuration drift detection is critical.
- Have you audited cellular modems and other out-of-band connectivity that may provide unmonitored internet paths into your OT network?
Defensive Recommendations
Based on the joint advisory and aligned with CISA’s Cross-Sector Cybersecurity Performance Goals (CPGs 2.0), the following actions are prioritized:
Immediate (24–72 Hours)
- Disconnect PLCs from public-facing networks. This is the single most impactful action. No PLC should be directly reachable from the internet under any circumstances.
- Audit all external-facing ports on OT network segments for 44818, 2222, 102, 22, and 502.
- Disable default credentials on all PLCs, HMIs, and network infrastructure in OT environments.
- Verify offline backups of PLC project files and configurations exist and are tested.
- Review remote access pathways — identify every VPN, cellular modem, and vendor maintenance connection into OT networks.
Short-Term (1–4 Weeks)
- Enforce multi-factor authentication on all remote access to OT environments.
- Deploy VPN, firewall, and proxy controls between enterprise IT and OT zones.
- Implement passive network monitoring on control system networks to detect anomalous ICS protocol traffic.
- Baseline PLC configurations and establish automated drift detection.
- Disable unused services and ports on all OT network devices.
Ongoing
- Conduct regular vulnerability scans and asset exposure assessments of OT environments.
- Exercise and test incident response plans that explicitly address loss of control system integrity — not just data confidentiality.
- Map security controls to MITRE ATT&CK for ICS techniques referenced in the advisory.
- Monitor for IoCs published in the advisory across both IT and OT network telemetry.
- Engage with sector-specific ISACs for updated threat intelligence during periods of elevated geopolitical risk.
Architecture Implications
This attack exploits the most fundamental architectural failure in OT security: direct internet exposure of control system devices without intermediary security controls.
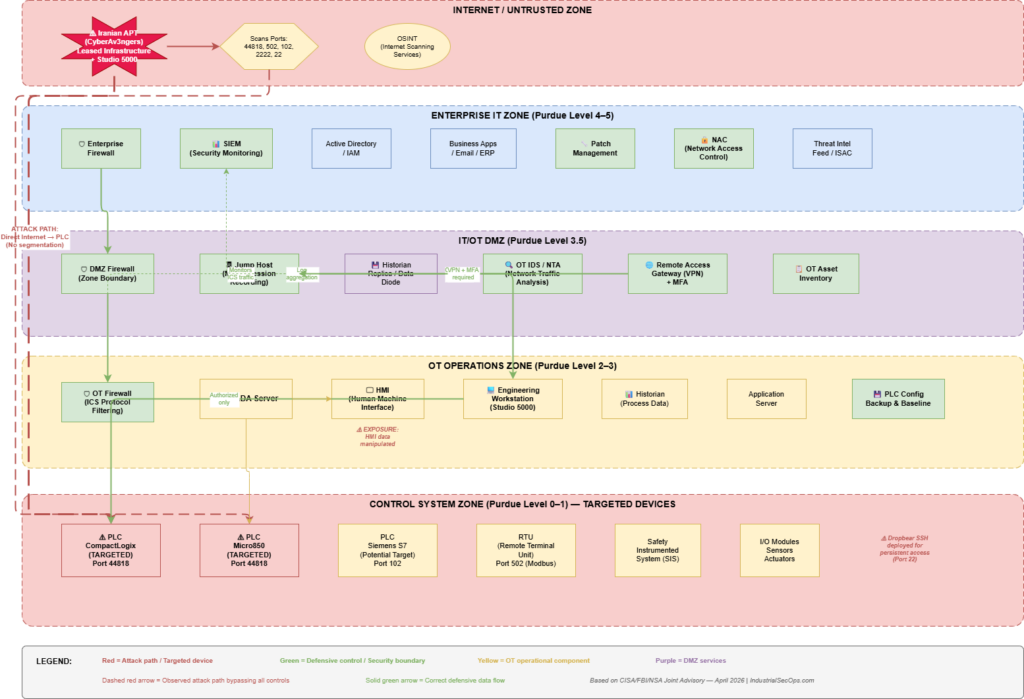
A properly segmented OT architecture based on the Purdue Model / IEC 62443 zones and conduits should ensure that:
- Level 0–1 devices (PLCs, RTUs, sensors, actuators) are never directly reachable from untrusted networks
- A DMZ separates the enterprise IT network from OT operations, with all traffic passing through defined conduits with inspection
- Engineering workstation access to PLCs is tightly controlled, logged, and limited to authorized personnel on authorized workstations
- Remote access is routed through a hardened jump host in the DMZ, with MFA, session recording, and time-limited access
- Historian and data replication services operate in the DMZ, preventing direct queries from IT into OT
- Network monitoring and anomaly detection (IDS/NTA) are deployed at zone boundaries to detect unauthorized ICS protocol traffic
- Asset inventory provides a continuously updated view of all OT devices, firmware versions, and network exposure
The below architecture diagram maps these controls to the specific threat described in this advisory, highlighting the exposure points and defensive control positions.
Key Takeaways
- Internet-exposed PLCs are being actively compromised by nation-state actors. This is confirmed, ongoing, and causing real operational damage.
- No exploit is required. The attackers use legitimate engineering software against improperly exposed devices. Reduce the attack surface, not just patch vulnerabilities.
- Detection is hard when adversaries use legitimate tools. Invest in network monitoring, configuration baselining, and anomaly detection — not just signature-based controls.
- The Purdue Model exists for exactly this reason. Proper network segmentation with enforced zone boundaries would have prevented every observed attack in this campaign.
- Geopolitical tension translates directly to OT risk. Critical infrastructure operators must maintain elevated monitoring during periods of international conflict.
- Manufacturers must deliver secure-by-default products. PLCs that accept unauthenticated connections from any client with the right software are insecure by design.
- Incident response plans must address control system integrity. Restoring a compromised PLC is not the same as reimaging a compromised server.
Conclusion
This joint advisory is a clear signal: the era of theoretical OT threats is over. Nation-state actors are actively compromising PLCs in production environments, manipulating control logic, and causing operational disruption across US critical infrastructure.
The defenses are not mysterious. Disconnect PLCs from the internet. Segment your networks. Monitor for anomalous connections. Baseline your configurations. Enforce authentication. Test your recovery procedures.
Every one of these actions is within the capability of any organization operating industrial control systems. The question is not whether defenders know what to do — it is whether they will do it before the next intrusion moves from disruption to damage.
For OT defenders: treat this advisory as a direct tasking. Validate your architecture. Close your exposure gaps. Prepare your response plans. The adversary is already inside the wire.
Published on IndustrialSecOps.com — Practical OT security intelligence for defenders who protect the systems that keep the world running.