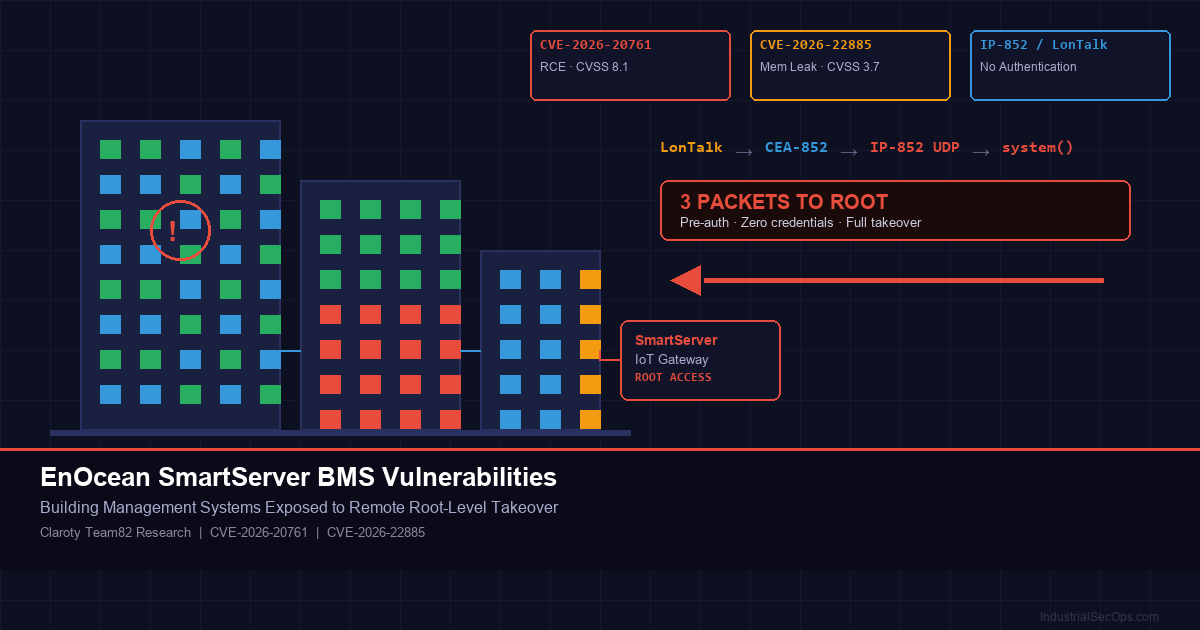
When Your Building Fights Back: EnOcean SmartServer Vulnerabilities Expose Building Management Systems to Root-Level Takeover
⚠️ TL;DR for Defenders
Two vulnerabilities in EnOcean’s SmartServer IoT platform (CVE-2026-20761 and CVE-2026-22885) allow remote, unauthenticated attackers to execute arbitrary commands with root privileges on building management system controllers. The flaws exploit improper input validation in the IP-852 protocol — a legacy building automation standard retrofitted for internet connectivity. Successful exploitation gives attackers full control over HVAC, lighting, power distribution, and physical security systems. EnOcean has released a patch (v4.60.023). If you operate SmartServer IoT or legacy i.LON devices, update immediately.
What Happened
On April 29, 2026, Claroty’s Team82 vulnerability research group disclosed two security vulnerabilities in EnOcean’s SmartServer IoT platform — a multi-protocol gateway and edge controller widely used to connect building automation devices to cloud management platforms.
The SmartServer IoT serves as the central nervous system for building management systems (BMS) in smart buildings, factories, data centers, and critical infrastructure facilities. It bridges legacy building protocols like LonTalk to IP networks, enabling centralized control of HVAC, lighting, access control, power monitoring, and environmental systems.
Team82 researchers found that the platform’s implementation of the CEA-852 standard — which tunnels the legacy LonTalk protocol over IP networks — contained critical flaws in how it processes incoming packets. The most severe vulnerability (CVE-2026-20761, CVSS 8.1) enables a remote, unauthenticated attacker to achieve full root-level code execution by sending a single malicious UDP packet.
| CVE | Type | CVSS v3 | Impact |
|---|---|---|---|
| CVE-2026-20761 | Remote Code Execution | 8.1 (High) | Pre-auth OS command injection → root shell |
| CVE-2026-22885 | Memory Leak / ASLR Bypass | 3.7 (Low) | Stack memory disclosure, enables ASLR bypass |
The vulnerabilities affect SmartServer IoT version 4.60.009 and earlier, as well as legacy Echelon i.LON controllers. EnOcean has released SmartServer 4.6 Update 2 (v4.60.023) to address both issues.
Technical Breakdown
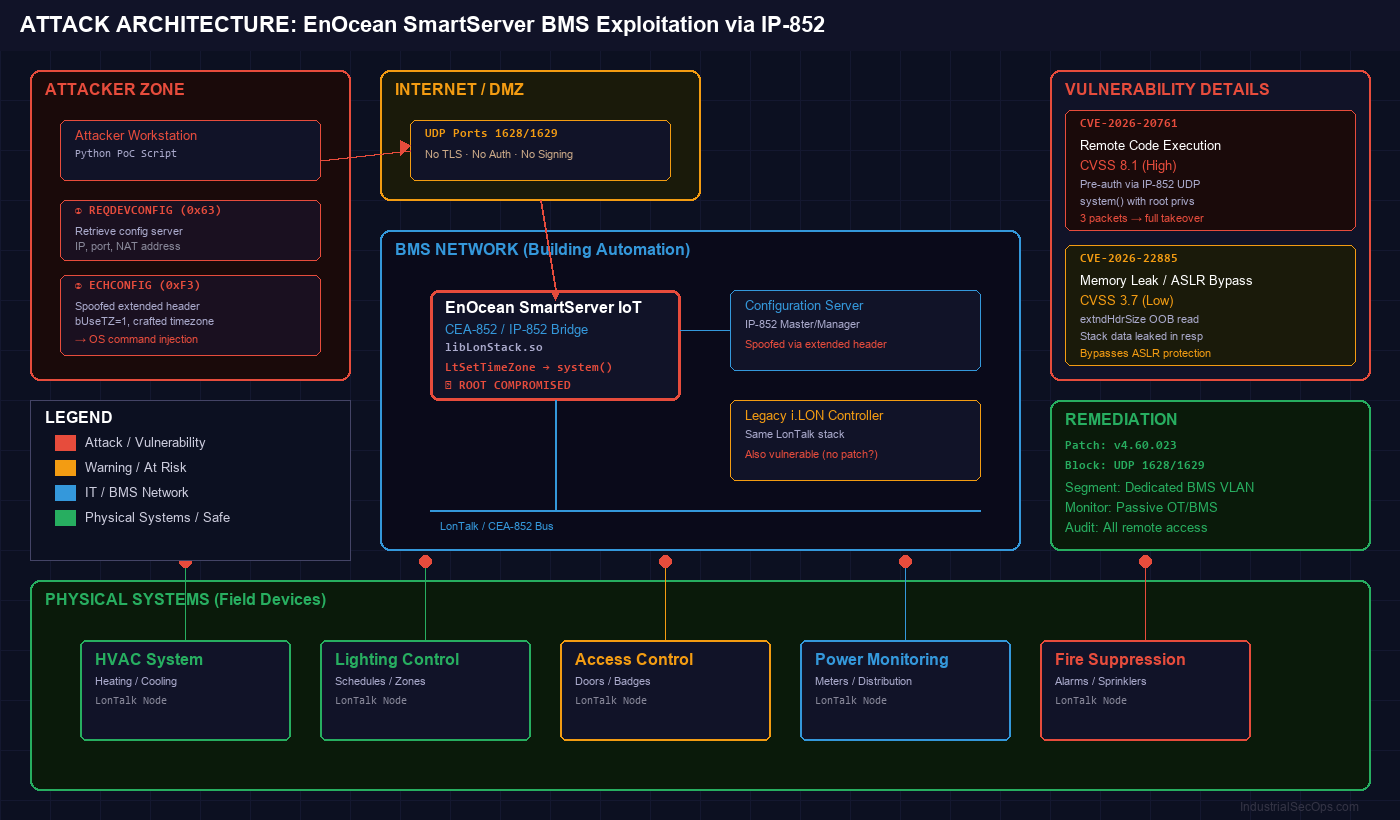
The Protocol Chain: LonTalk → CEA-852 → IP-852
Building management systems have historically relied on LonTalk, a protocol developed by Echelon Corporation in the 1990s for distributed control networks. As facilities modernized, the CEA-852 standard was created to tunnel LonTalk traffic over IP networks — enabling cloud connectivity and remote management.
EnOcean’s SmartServer IoT implements this CEA-852/IP-852 bridge. It listens for incoming IP-852 UDP packets on ports 1628/1629 and processes them through its LonTalk stack. This is where the vulnerabilities reside.
CVE-2026-20761: Pre-Auth Remote Code Execution
The critical vulnerability exists in the LtSetTimeZone function within the SmartServer’s LonTalk library. This function constructs a shell command from a timezone string received via IP-852 packets and passes it directly to the Linux system() call — with root privileges.
Attack Chain — Three Packets to Root
- Reconnaissance — Send a standard device configuration request to retrieve the SmartServer’s configuration server details. No authentication required.
- Impersonation — Construct a crafted IP-852 packet with an extended CNIP header that spoofs the configuration server, bypassing origin verification.
- Command Injection — Send a malicious configuration packet containing a crafted timezone string that breaks out of shell quoting and injects arbitrary commands.
- Result — The SmartServer processes the packet and executes the injected commands as root.
CVE-2026-22885: ASLR Bypass via Memory Leak
A second vulnerability enables attackers to leak stack memory by sending crafted IP-852 time synchronization packets. The flaw lies in how the IP-852 header parser handles the extended header size field — by supplying an unexpected value, an attacker forces the controller to read from an out-of-bounds stack offset and echo it back in the response.
This memory leak can expose runtime function pointers, enabling an attacker to calculate library base addresses and bypass ASLR (Address Space Layout Randomization) — a critical operating system defense mechanism.
A Hidden Vulnerability
Key finding: The vulnerable LtSetTimeZone function is not present in the open-source version of the LonTalk stack published on EnOcean’s GitHub. It exists only in the compiled binary library shipped on devices. This means the vulnerability is invisible to source code review — only binary analysis of on-device firmware would reveal it.
Who Is Affected
Directly affected products:
- EnOcean SmartServer IoT — version 4.60.009 and earlier
- Legacy Echelon i.LON 100/600 controllers
- Any device implementing CEA-852 with Echelon proprietary packet types
| Sector | BMS Use Case | Impact of Compromise |
|---|---|---|
| Commercial Real Estate | HVAC, lighting, elevator control | Tenant safety, energy waste |
| Data Centers | Precision cooling, power distribution | Server overheating, equipment damage, outages |
| Manufacturing | Environmental controls, clean rooms | Product contamination, production halts |
| Healthcare | Operating room climate, pharmacy storage | Patient safety, drug storage compliance |
| Defense / Government | Secure facility environmental controls | Physical security compromise |
| Critical Infrastructure | Substations, water treatment, power plants | Safety system disruption, cascading failures |
Why This Matters
BMS Is the Forgotten OT Attack Surface
Building management systems occupy a dangerous blind spot in most organizations’ security posture. They are operational technology by every definition — they control physical processes, affect human safety, and operate on legacy protocols — yet they typically fall outside the scope of both IT security teams and OT security programs.
BMS devices are often:
- Managed by facilities teams, not security teams
- Connected to both IT and OT networks, creating bridge points
- Running decades-old protocols — LonTalk has been in use since the 1990s
- Exposed to the internet for remote management without proper segmentation
- Excluded from vulnerability scanning and patch management programs
Legacy Protocols, Modern Connectivity
The CEA-852 standard exemplifies a recurring OT security pattern: taking a protocol designed for isolated, trusted networks and retrofitting it for IP connectivity without adding authentication or integrity checks. The IP-852 packets that trigger these vulnerabilities are plain UDP — no TLS, no authentication, no message signing. Anyone who can reach port 1628 or 1629 on a SmartServer can send the attack packets.
Physical Safety Consequences
Unlike IT compromises that result in data theft, BMS attacks can directly affect the physical environment:
- Disabling HVAC in a data center can cause thermal cascading failures costing millions
- Manipulating access control can enable physical intrusion
- Altering environmental controls in pharmaceutical production can compromise products
- Disrupting fire suppression or emergency ventilation can endanger lives
MITRE ATT&CK for ICS Mapping
| Tactic | Technique | ID | Application |
|---|---|---|---|
| Initial Access | Exploitation of Remote Services | T0866 | Exploiting SmartServer IP-852 listener without authentication |
| Execution | Unauthorized Command Message | T0855 | Injecting OS commands via crafted timezone packet |
| Persistence | Program Download | T0843 | Root access enables persistent backdoor installation |
| Collection | Theft of Operational Information | T0882 | Memory leak exposes stack data and runtime addresses |
| Impact | Loss of Availability | T0826 | Disrupting BMS controller disables building systems |
| Impact | Manipulation of Control | T0831 | Root access allows modification of BMS logic and setpoints |
Defensive Recommendations
🚨 Immediate (24-48 Hours)
- Patch now — Update SmartServer IoT to version 4.60.023 or later. This is a pre-auth RCE with a public PoC.
- Identify all BMS controllers — Locate every SmartServer IoT and i.LON device across your facilities. Many organizations don’t have complete BMS asset inventories.
- Block IP-852 from untrusted networks — Ensure ports 1628/1629 (UDP) are not reachable from the internet or untrusted network segments.
- Check for exposure — Search Shodan/Censys for your IP ranges with IP-852 / LonTalk service fingerprints.
⏲ Short-Term (1-4 Weeks)
- Segment BMS networks — Place all building automation controllers in a dedicated VLAN with strict firewall rules. BMS should never share a subnet with general IT.
- Deploy network monitoring — Implement passive OT/BMS network monitoring to detect anomalous IP-852 traffic patterns and unauthorized configuration changes.
- Audit remote access — Review all remote management pathways to BMS controllers. Replace direct internet exposure with VPN or jump-host architectures.
- Inventory legacy devices — Catalog all Echelon i.LON controllers. Legacy devices may not receive patches and require compensating controls.
🛠 Long-Term (1-6 Months)
- Include BMS in OT security program — Building automation must be covered by the same vulnerability management, monitoring, and incident response programs as industrial control systems.
- Establish BMS security governance — Define ownership: who is responsible for patching, monitoring, and securing building automation controllers?
- Evaluate protocol migration — For facilities with extensive LonTalk/CEA-852 deployments, evaluate migration to modern protocols with built-in authentication and encryption (e.g., BACnet/SC).
- Conduct BMS penetration testing — Engage OT-specialized security firms to test building automation environments. Most have never been assessed.
IndustrialSecOps Analyst Assessment
Severity Rating: HIGH
Bottom line: These vulnerabilities turn a building management controller into an attacker’s root shell with three UDP packets and zero authentication. The SmartServer IoT sits at the intersection of IT and OT networks in facilities ranging from commercial offices to data centers and critical infrastructure — making it a high-value pivot point. The availability of a public proof-of-concept exploit means the window for patching before exploitation is narrow. More broadly, this research spotlights BMS as an under-defended OT domain that most security programs systematically overlook. If your organization operates buildings with automated systems, this is your signal to bring BMS into your security program.
Sources and Further Reading
- Claroty Team82, “Exploiting EnOcean SmartServer to Attack Connected Building Management Systems,” April 29, 2026 — claroty.com
- SecurityWeek, “EnOcean SmartServer Flaws Expose Buildings to Remote Hacking,” April 30, 2026 — securityweek.com
- Claroty Team82, “The Risky Road Bringing Building Management Systems Online: Exploring the CEA-852 Standard” — claroty.com
- Claroty Team82, “Examining the Legacy BMS LonTalk Protocol” — claroty.com
- EnOcean SmartServer IoT Release Notes — v4.60.023 — enoceanwiki.atlassian.net
- CVE-2026-20761 — Claroty Disclosure Dashboard
- CVE-2026-22885 — Claroty Disclosure Dashboard